As far as I can see now, 2009 will be the year of exploits for electronic and electro-mechanical locks. As you can read on Marc Tobias his blog they will talk about some exploits against these kind of locks at Defcon. And so will Han Fey and me (in more detail) at the HAR conference two weeks after Defcon.
And there are others doing the same thing. Take for example a mysterious group calling themselves ‘lockbeepers’. They just published a report about the Burgwächter TSE 3000, showing two interesting attack vectors.
The lockbeepers seem to have had a hell of a time analyzing it as you can read in their report (PDF).
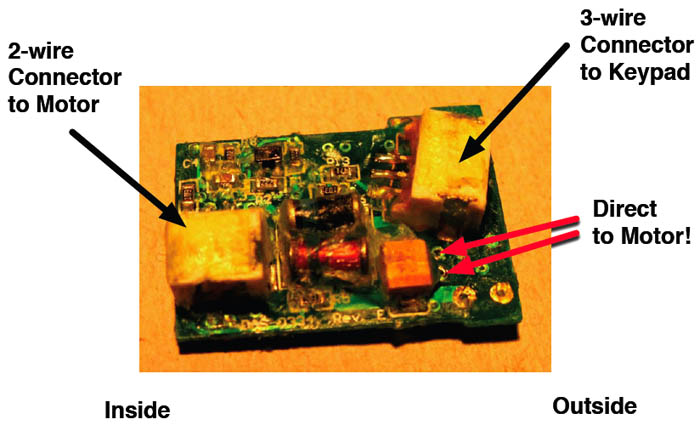
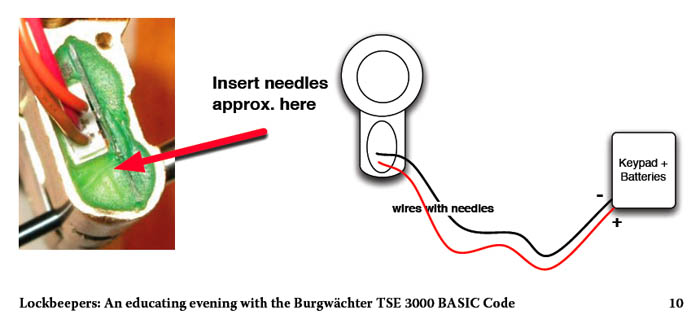
In the report they explain two possible ways of attacking this lock. The first attack is locating the cable the pin numbers are being transported by (in the clear). Hooking up a small chip on that line would allow anyone to record and replay the pin-numbers captured.
The second attack is more practical: it shows you where to apply power on the circuit board and open the lock. According to the lockbeepers it is not difficult to reach that point.
I would like to thank the lockbeepers for their document and hope to see more work from their hands. If they do you will most likely read it on blackbag …

I was wandering what the subject of the HAR talk would be!
Looking forward to it.
In Black Hat security conference was demo of interesting way to grab keyboard (computer) data, maybe usable whit some locks?
http://www.networkworld.com/news/2009/070909-electrical-data-theft.html?source=NWWNLE_nlt_daily_pm_2009-07-09
eena, the problem is that the locks usually are not supplied from electrical grid and when they are, they have a floating source and thus there is no earth connection to spy from.
I cannot tell you how miserable I am to miss HAR. I will wait with baited breath for videos after the fact. I know your presentations will be excellent, and good luck to everyone in the Open (and other competitions) as well!