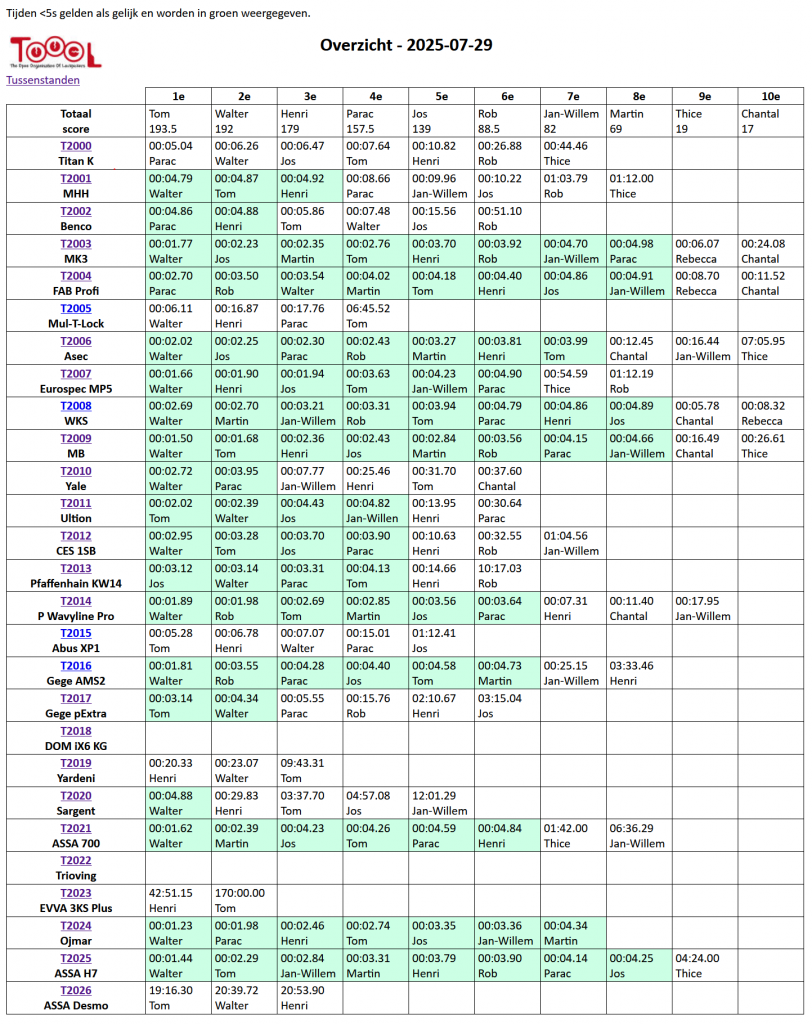
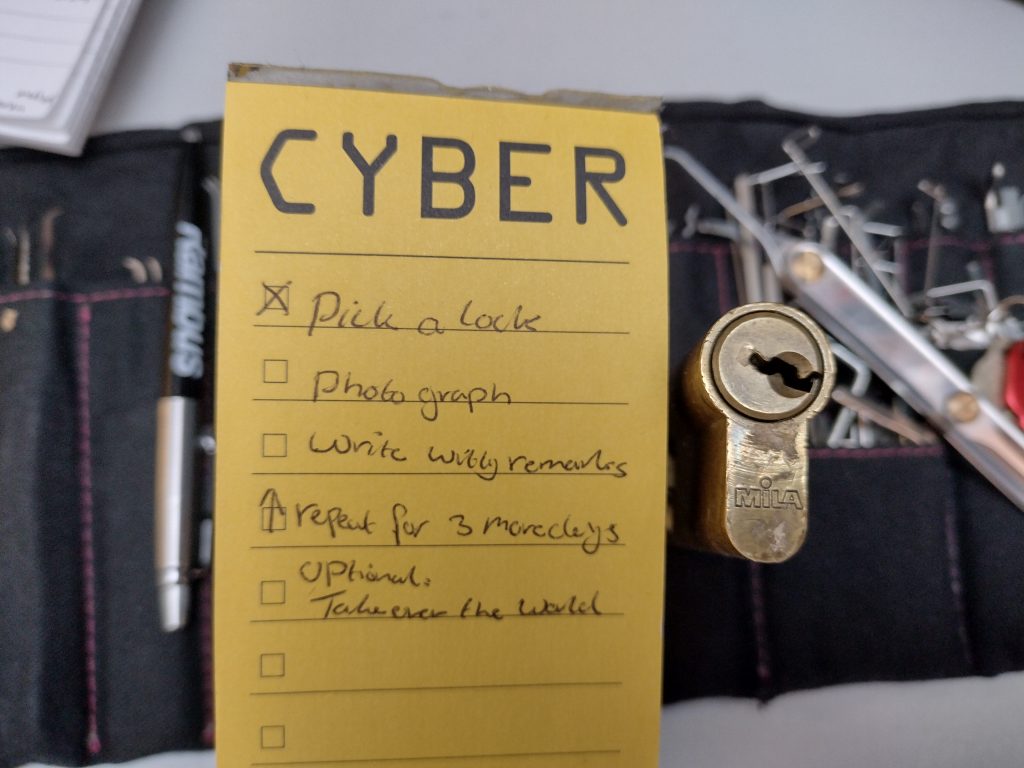
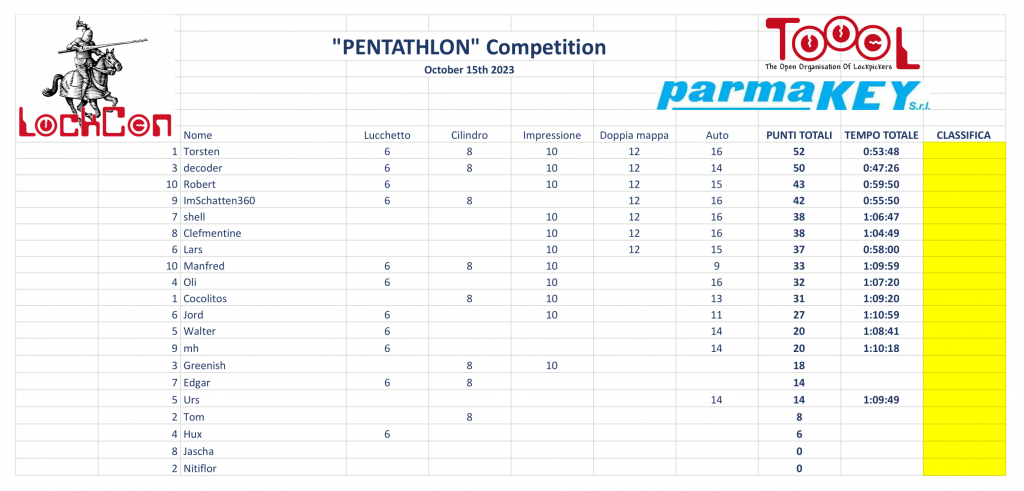
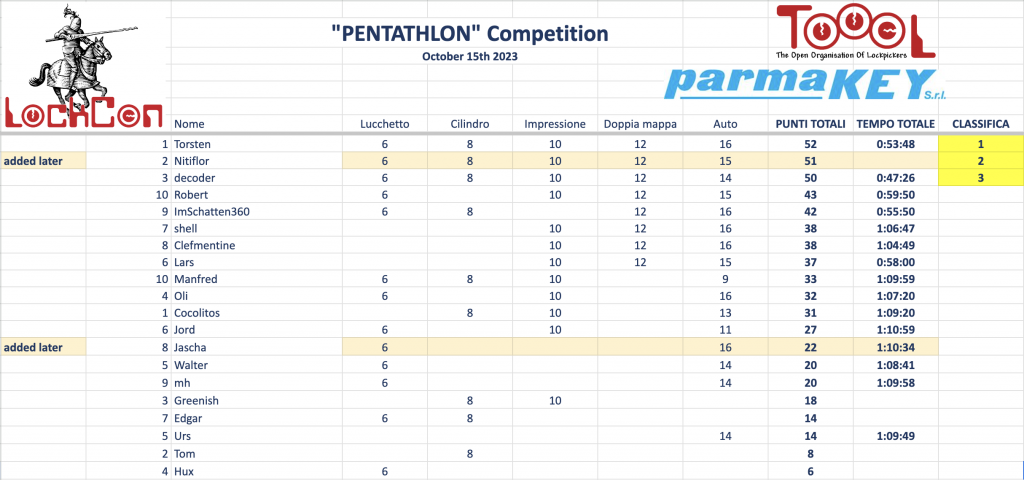
The Toool lockpicking competition is held yearly from 2004 onwards. About 25 locks are selected and it is up to the Toool members to try and pick them at Toool gatherings. They can spend as much time as they like, and can retry to open a lock as often as they like. Scores are given out depending on opening speed, 10 points for the fastest person up to 1 point for the 10th time on the lock. Since some locks can be opened with just a single rake, times under 5 seconds all count as the same time.
Every year, locks are selected on what we think are good locks, meaning: they cannot be opened in a single rake, but can be opened within the year. This year, there were 26 locks and the mix looked like this:

Having won 18 of the 20 competitions so far, I was keen to win again, but everybody is getting better! I am a very fast picker, but it is not just speed, it is also making sure you open all the locks. In the end, there were a few locks that were only opened by 5 or less people.
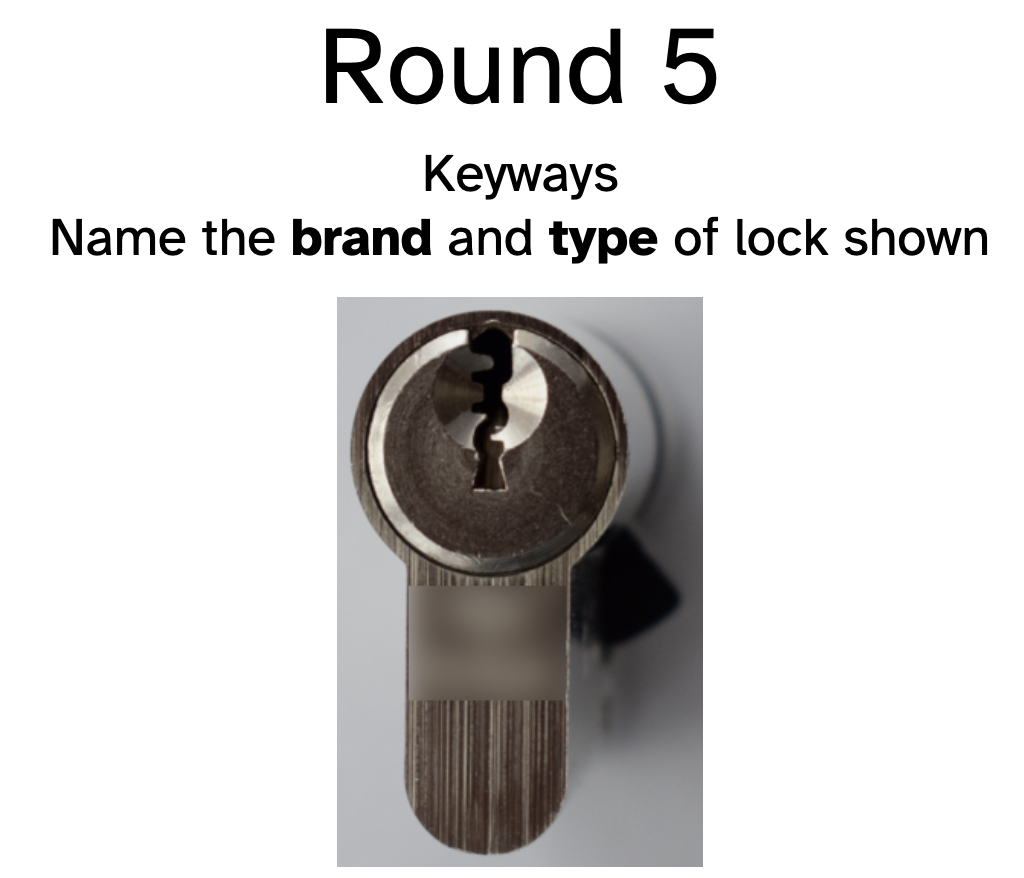
The Yardeni and Sargent looked simple, but turned out to be hard. The Abus XP1 was left unpicked for a long time, mainly because it has a reputation of being very hard to pick. When it turned out to be (quickly!) pickable, it got 5 openings.
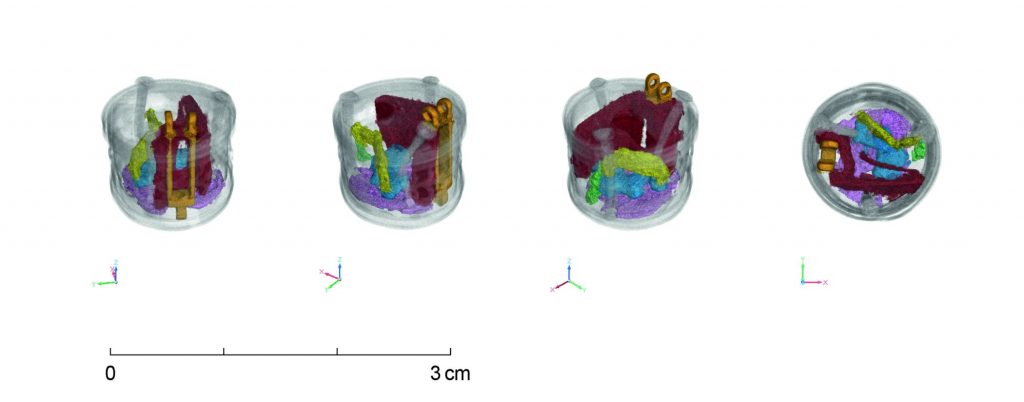
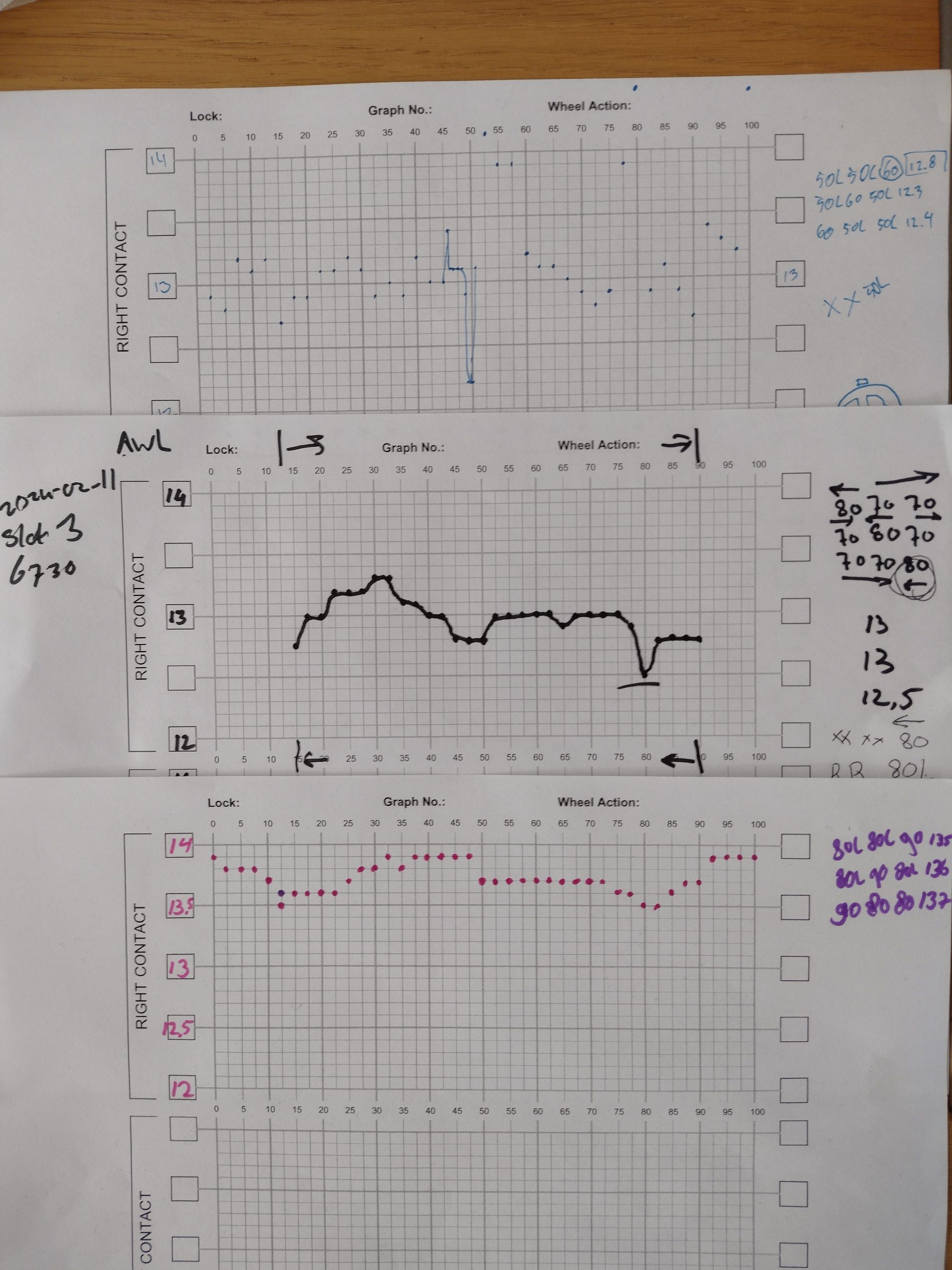
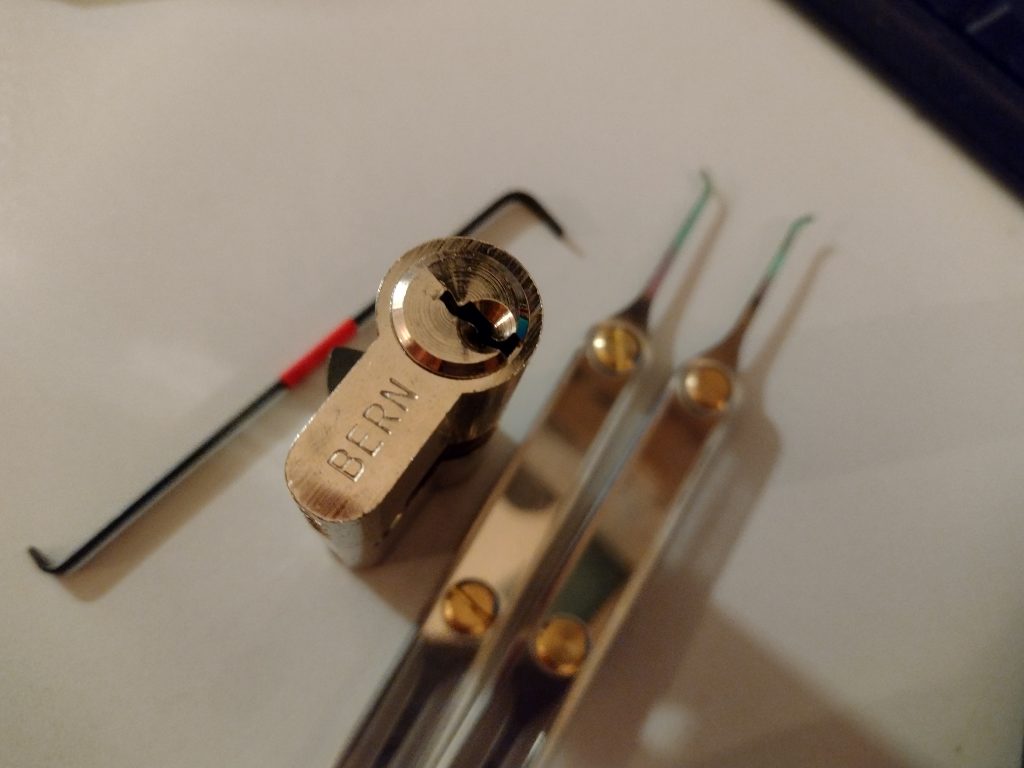
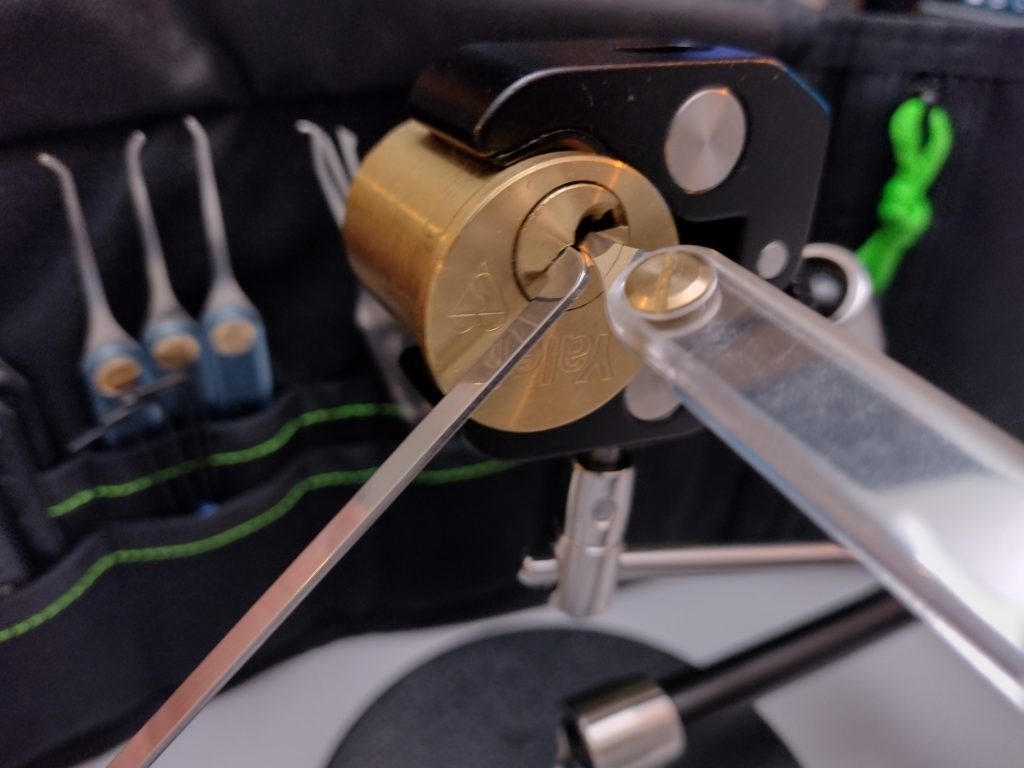
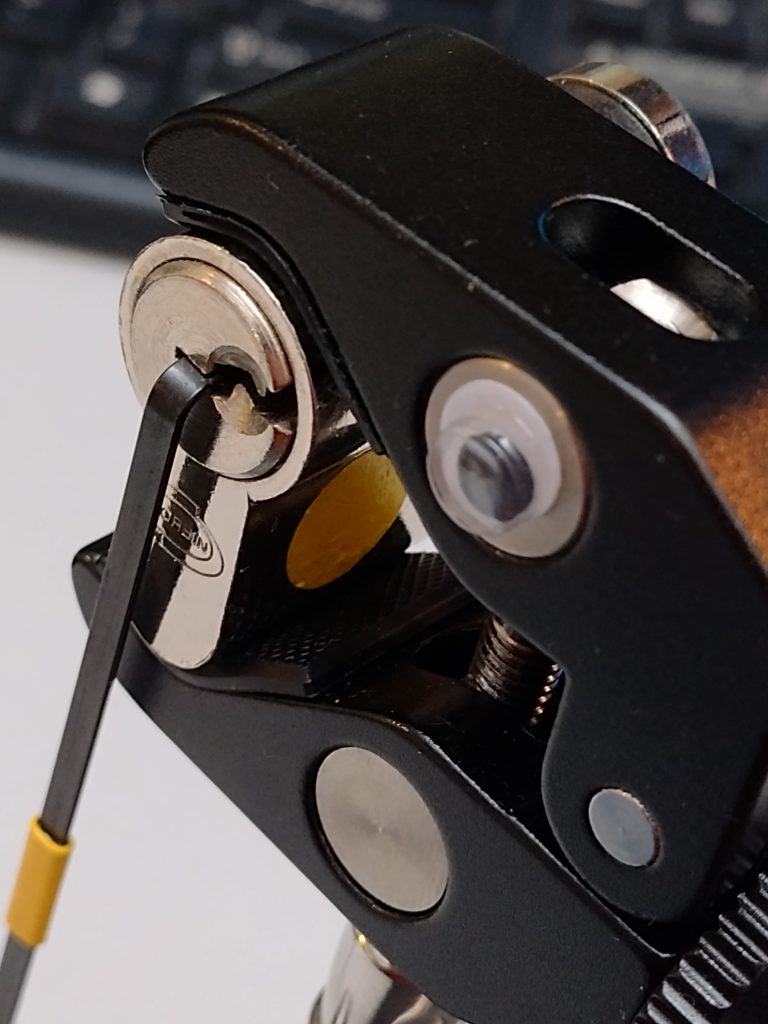
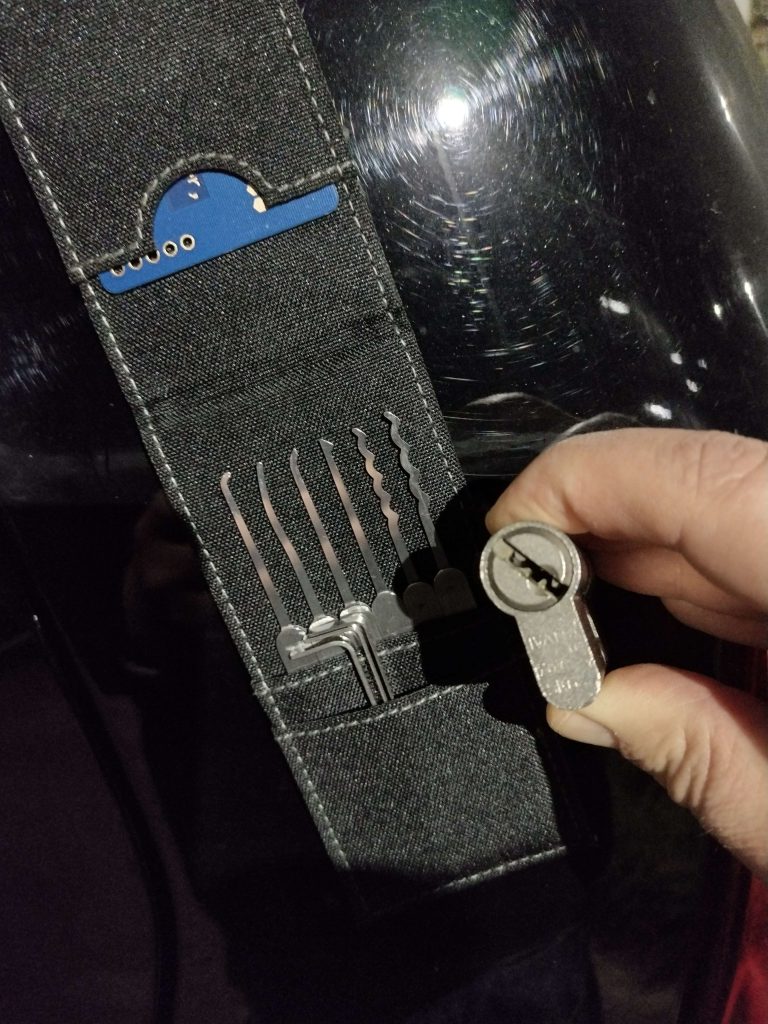
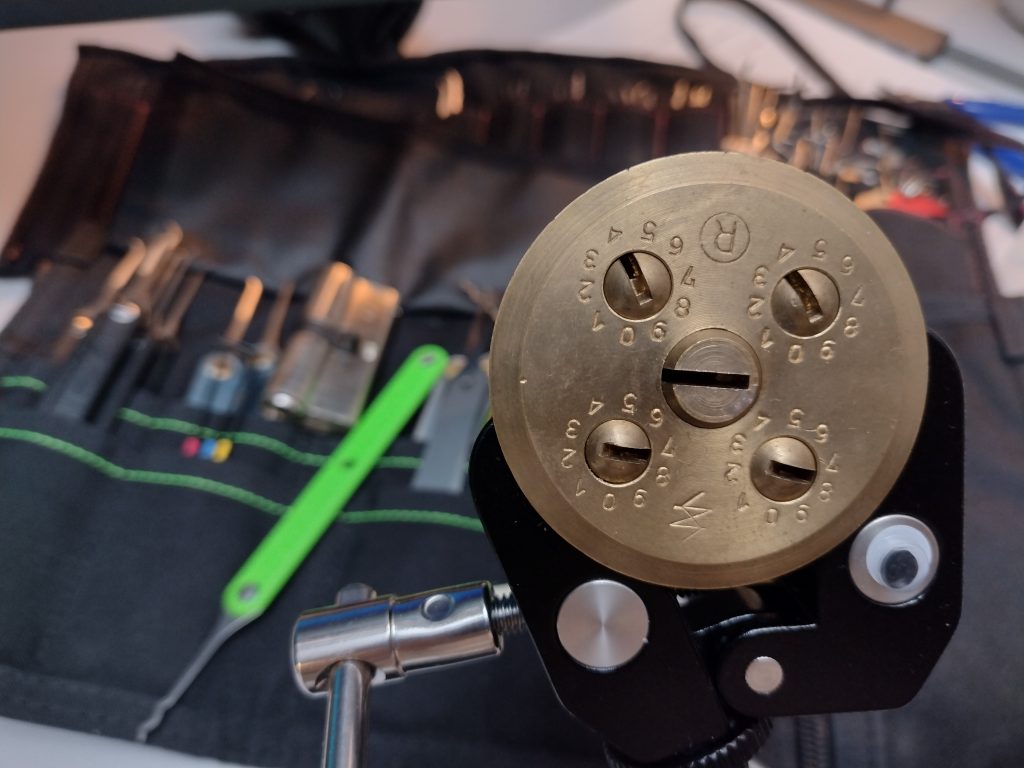
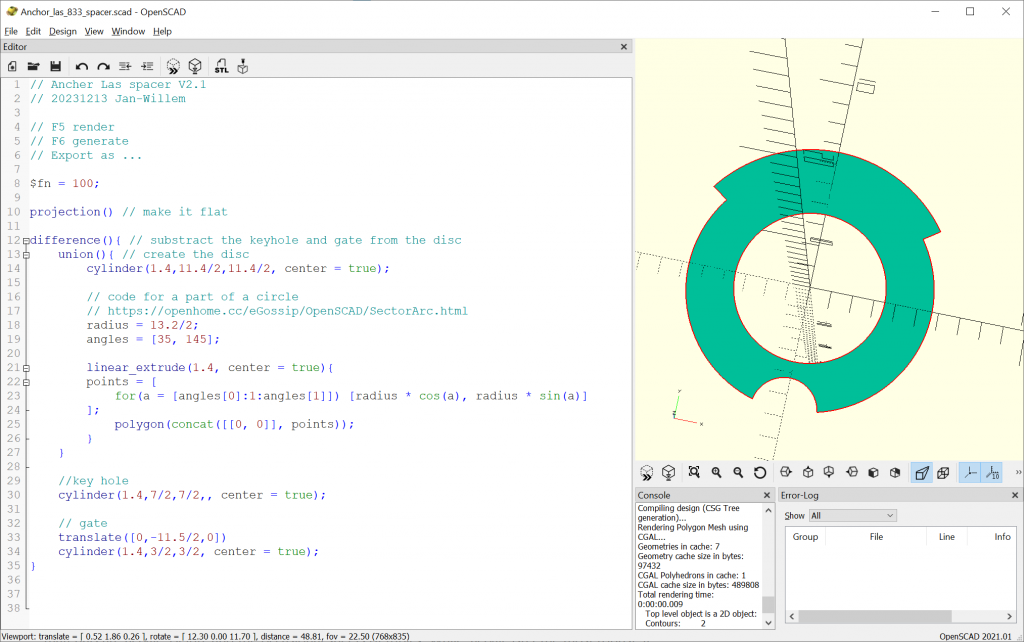
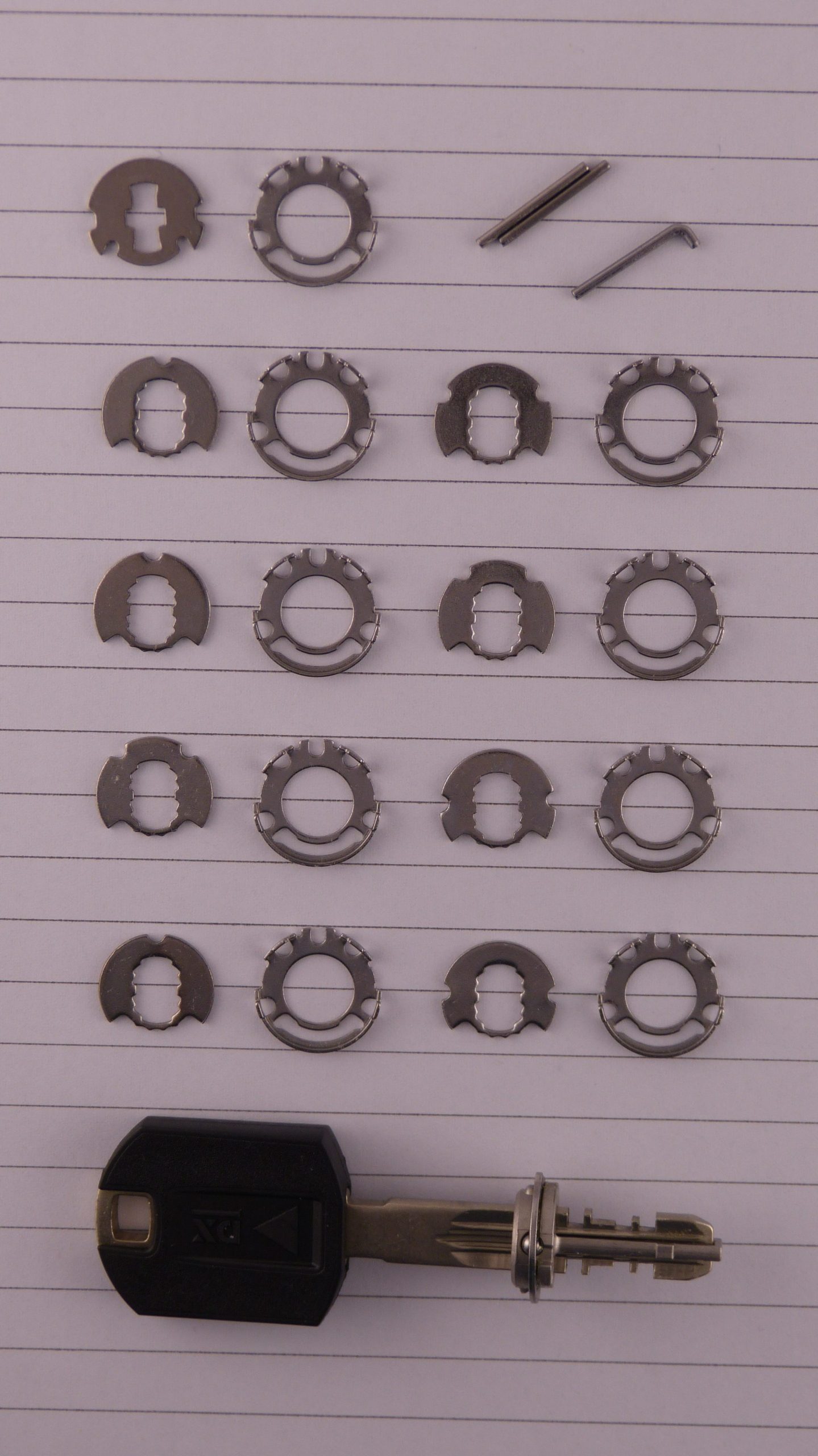
Then to the hardest locks. The EVVA 3KS was my personal nemesis. There is only so much time you can practice on these locks (only during gatherings). For the first time, I resorted to practicing at home. I took an EVVA 3KS I had in my collection, created specialised picking tools and practiced until I could open it. However, the 3KS in the competition would not budge. The main problem being that, when moving some sliders, the lock would reset (which my own 3KS would not do). I’ve spent quite a few hours on this 3KS to no avail. It was opened by Henri who became third, and by Tom who won this year’s competition by 1.5 point. Congratulations Tom! The three of us opened the same locks (except the 3KS for me) but I scored higher than Henri because of my fast openings on the locks I did open.
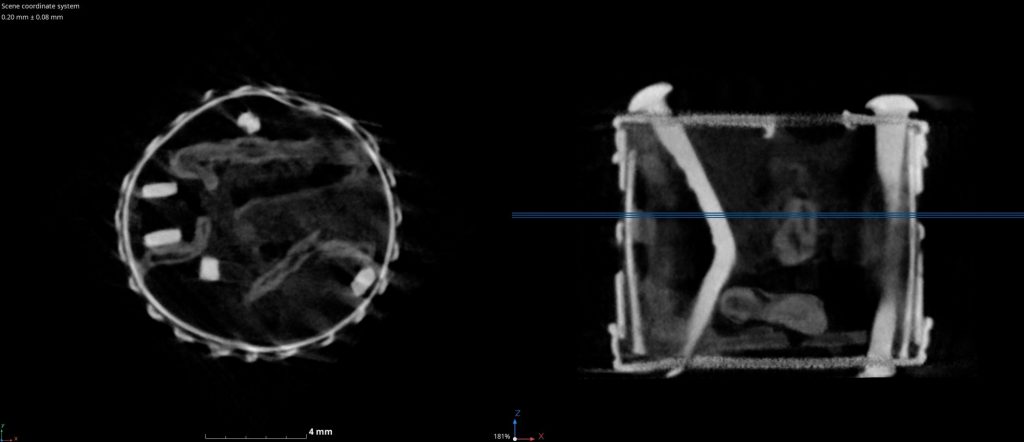
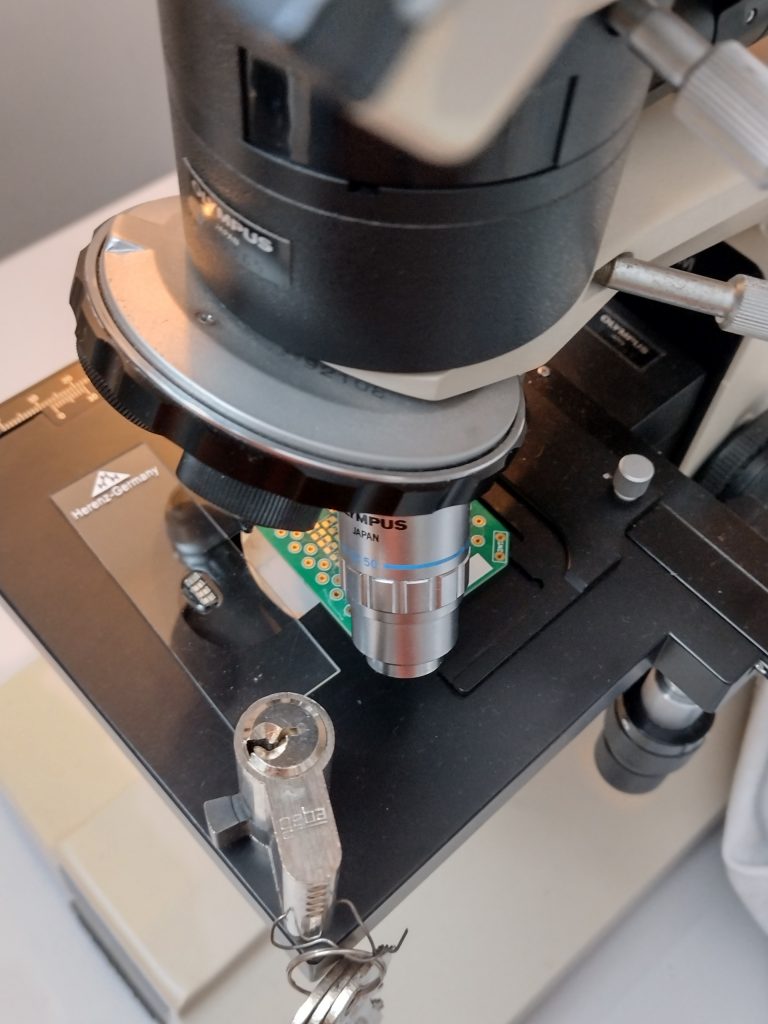
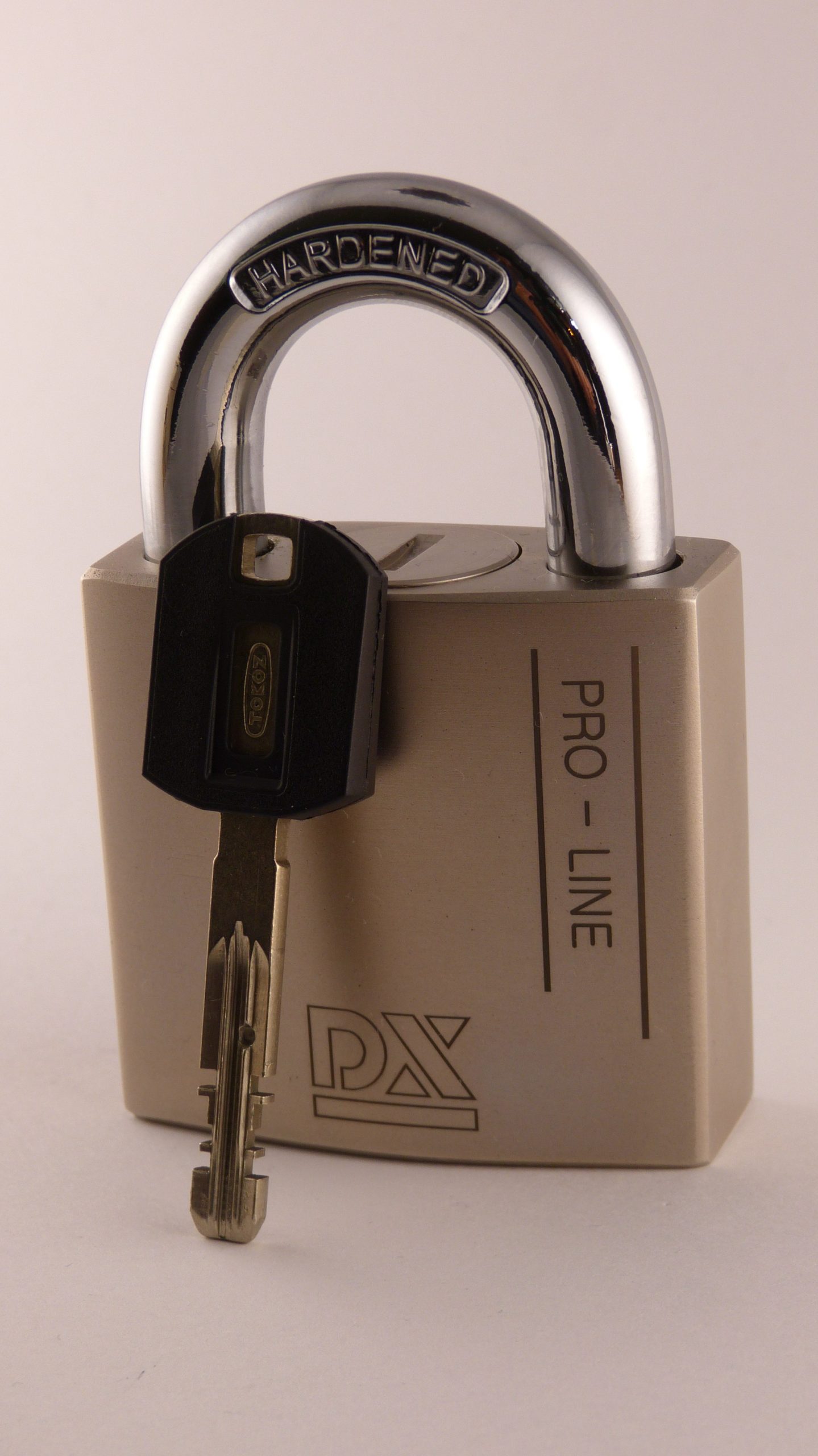
Since a 3KS is easy to disassemble without having the key, I took a look at the insides, to see if there was anything that can explain the resetting of the lock, but everything in there seemed very normal.

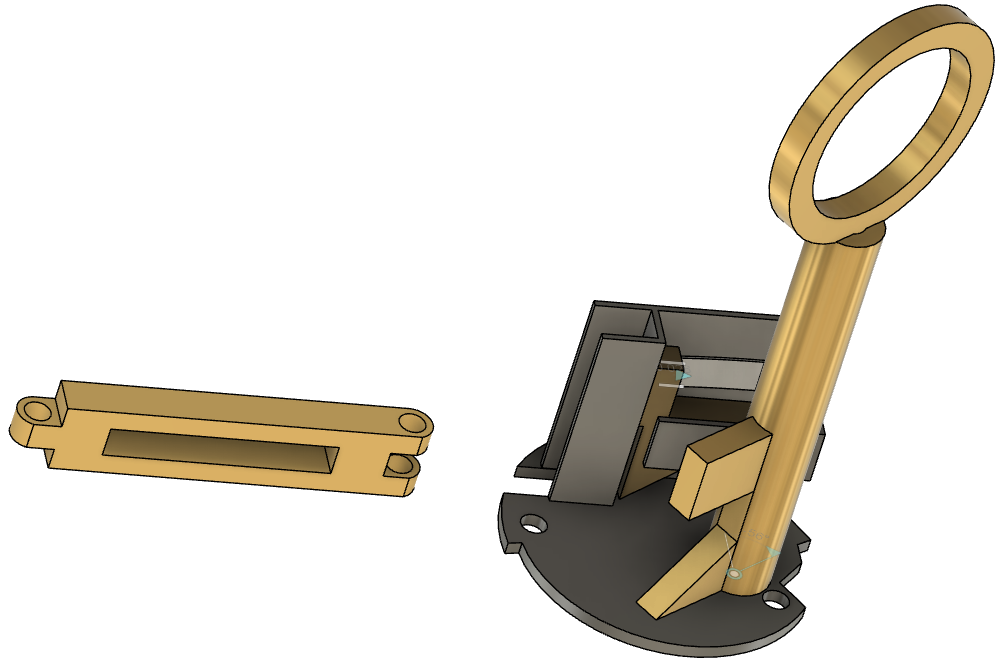
These are the two locks that no-one opened. The TrioVing does give feedback while picking, but nobody succeeded in opening it. The DOM was picked into a false set but also never opened. The pins have a shape that makes picking quite hard.
I am looking forward to the next competition. This one was exciting right until the end. The last gathering I decided to not work on the 3KS but try and gather a few points by improving times on simpler locks. At the start of the gathering, I was only half a point in the lead, and was able to gain another point by improving my time on the Benco lock. The Benco I don’t like, as I don’t really get a good feel of how to pick it. Tom was trying to open a new lock (such as the DOM above) for maximum points, but then changed strategies and improved his time on the Desmo, giving him a 1.5 point lead. I only realise now, writing this, that improving my time on the Benco with another 2 seconds would again have been enough for the win. That is how close this years’ competition was!
If you have locks you are willing to part with, please consider donating them to Toool for the next Toool NL competition. We are particularly looking for the difficult locks. Equivalent to Desmo, 3KS, Trioving, and IX6. As we are building two cases, one for us and one to share with other Toool organizations, two locks would be ideal.
Walter.